Protecting the Systems That Keep the World Running
Industrial control systems (ICS) are embedded in the fabric of critical infrastructure, including water utilities, power grids, critical manufacturing, oil and gas pipelines, and data centers that host artificial intelligence workloads increasingly shaping modern life. These are the systems that drive the socio-economic engine of nations. When they fail, the consequences cascade: forced shutdowns, equipment damage, service outages, and in the worst case, threats to human safety.
The attack surface for these systems is expanding. Adversaries are no longer just targeting Information Technology (IT) networks they are reaching deeper into the operational technology (OT) stack, manipulating programmable logic controllers (PLCs), spoofing sensor signals, and exploiting the gap between network-centric defenses and the physical processes those defenses were never designed to protect. The critical need for trained cybersecurity professionals who understand both the digital and physical dimensions of these systems has never been more urgent.
At Ohio University's ITS Cybersecurity Labs, we are building the research capability and the workforce to meet that need. Our work spans ICS virtualization, multi-vendor PLC security testing, process-aware threat modeling, hardware-rooted trust, and AI-driven intrusion detection, all under one roof, all focused on one mission: securing the infrastructure that society depends on.
Here is what we do and why it matters.
1. Industrial Control System Virtualization: Bringing Critical Infrastructure Into the Classroom
A fundamental challenge in ICS cybersecurity education is access. You cannot hand students the keys to an operational water treatment facility or a live power substation and ask them to find the vulnerabilities. The consequence of a mistake in a live environment is real and unacceptable.
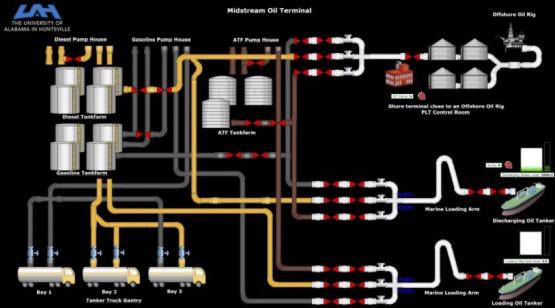
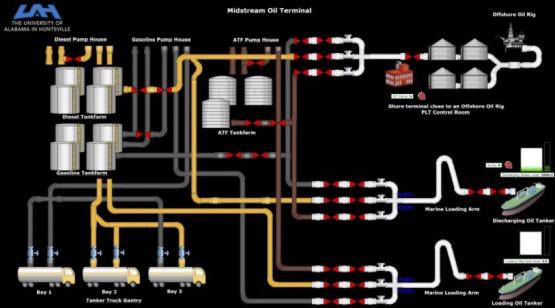
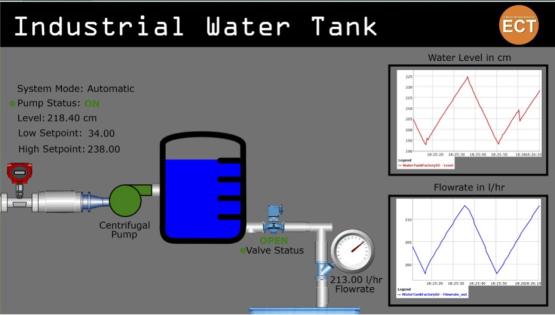
To bridge this gap, Dr. Rishabh Das developed a virtualization framework during his Ph.D. research under Dr. Tommy Morris, Director of the Center for Cybersecurity Research and Education (CCRE) and eminent scholar at the University of Alabama in Huntsville. The framework creates high-fidelity virtual models of real-world industrial processes, water tanks, gas pipelines, oil terminals, and heat exchangers that replicate the behavior of physical systems controlled by PLCs communicating over standard industrial protocols such as Modbus TCP.
Dr. Das under the supervision of Dr. Morris at UAH)
These virtual testbeds provide students with hands-on experience in controlling industrial processes, troubleshooting faults, and identifying cyber intrusions in environments that would otherwise be completely unavailable in most educational settings. Students across multiple universities, including several cybersecurity courses at Ohio University, actively use these models to study and secure critical infrastructure.
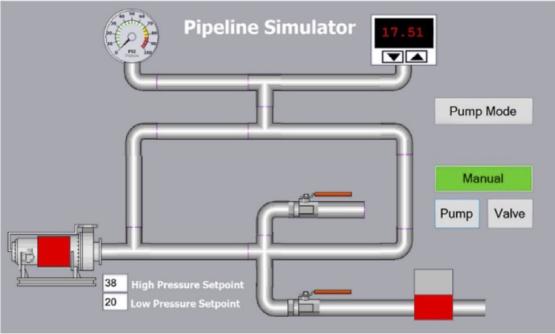
With recent funding from the National Institute of Standards and Technology (NIST), the Ohio University ITS Cybersecurity Labs continue to expand this testbed's capabilities by building virtual models of modern systems, including smart manufacturing environments, data center cooling infrastructure, and water filtration plants. These models serve a dual purpose: they bring immersive, experiential learning into the classroom, and they open research opportunities to study how adversaries can compromise the processes that underpin modern infrastructure.
Recent Virtual models

2. Multi-Vendor PLC Stack: Testing Intrusion and Defense Across Industrial Platforms
In the real world, no two industrial facilities run the same hardware. A water utility may deploy Allen-Bradley controllers, a manufacturing plant may standardize on Siemens S7 PLCs, and a smaller operation may rely on Modicon or Click hardware. Each vendor brings its own software stack, programming environment, and set of security assumptions. An attacker who understands these differences can exploit vendor-specific weaknesses that generic defenses miss entirely.
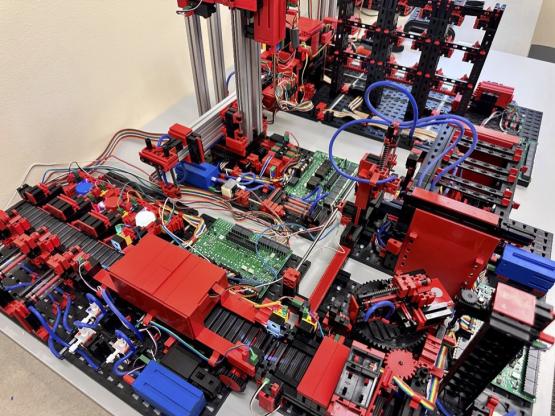
The ITS Cybersecurity Labs maintain a multi-vendor industrial computing research environment featuring PLCs from Siemens, Allen-Bradley, Modicon, Click, and the open-source OpenPLC platform. The Hardware environment is designed to answer a critical question: Do novel security principles generalize across vendors, or do they break when the underlying PLC architecture changes?

McClure School Information Networking Labs.
Students working in this environment gain holistic exposure to different industrial software stacks, learning how to program ladder logic across platforms and understanding the vendor-specific nuances that determine how control systems behave and where they are vulnerable. Researchers leverage the multi-vendor setup to validate security hypotheses under conditions that mirror the heterogeneous environments found in real-world critical infrastructure.
3. Threat Modeling: Understanding the Adversarial Mindset
Effective ICS defense starts with understanding the adversary. The ITS Cybersecurity Labs study emerging threat models structured around three core questions: How will an attacker compromise my critical asset? What will be impacted due to the cyberattack? And how can I mitigate the attack scenario?
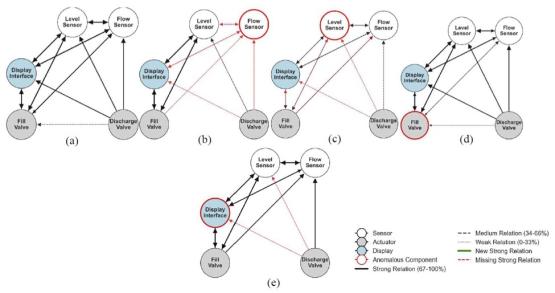
In our recent study published at IEEE AIIoT, our research team introduced a process-aware anomaly-detection framework that automatically baselines the behavior of industrial systems. Unlike signature-based approaches that rely on known attack patterns, this framework detects time-varying dependencies between process variables, capturing both stable and transient relationships between operational states. This allows it to identify deviations that traditional rule-based monitoring would miss.
The key insight is that the framework learns what "normal" looks like for a specific process and flags deviations from that baseline, even when the attack is designed to stay within expected signal ranges.
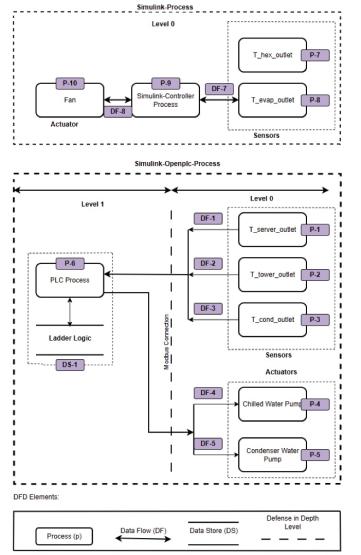
The team is also studying an increasingly critical target: modern data center cooling systems. As facilities hosting AI model training and cloud infrastructure become indispensable, understanding how adversaries can compromise cooling components and the cascading impact on operations represents an urgent research priority. A compromised cooling system does not just affect temperature; it can force computational workloads offline, damage hardware, and disrupt services at scale.
4. Hardware Security: Fingerprinting Industrial Systems with PUFs
Some of the most sophisticated threats to ICS operate entirely below the network layer. Supply chain attacks, hardware trojans, and physical-layer signal manipulation target the trust boundary between the digital control logic and the physical process it governs. Current network-centric defenses, such as firewalls, intrusion detection systems, and zero-trust gateways, provide no visibility into whether the sensor signals arriving at a PLC's I/O module are authentic or have been tampered with at the physical layer.
Ohio University is addressing this critical gap through novel hardware prototypes based on Physically Unclonable Functions (PUFs), a hardware security primitive that exploits inherent manufacturing variations in electrical circuits to generate unique, unforgeable device fingerprints. The core objective is to measure the trustworthiness of sensor and actuator signals entering industrial computers, providing a hardware-rooted trust anchor at the field layer where it is needed most.
This research, a collaboration between Dr. Ahmed Oun and Dr. Rishabh Das, was presented at IEEE ICCE 2026. The proposed architecture combines voltage fingerprinting with a temporal authentication protocol that integrates with standard ICS architecture without requiring modifications to vendor-specific PLC firmware. The system can detect injected anomalies, including spike faults, hard-over faults, and hardware trojan scenarios that push the system outside its safe operating envelope.
5. AI-Driven Cyber Defense: From Simulated Attacks to Real-Time Detection
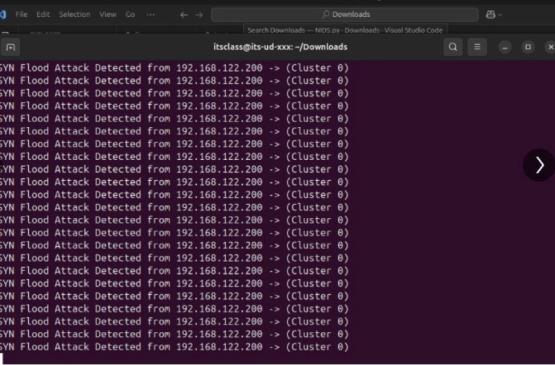
Artificial intelligence is not an abstract concept in our lab it is a tool that students learn to build, train, and deploy against real attack scenarios. Through experiential learning in the cyber defense course, students explore the full lifecycle of an intrusion detection system (IDS): from attack simulation to data collection, feature engineering, model training, and real-time deployment.
The workflow is designed to mirror real-world security operations. Students simulate attacks on industrial processes running in the lab's virtual testbeds, collect process and network data generated by those attacks, train machine learning algorithms to discriminate between normal operations and adversarial activity, and then deploy the trained models to detect attack scenarios in real time. A significant portion of this pipeline is taught in the classroom, giving students direct experience with the end-to-end workflow that underlies modern AI-driven cyber defense in ICS environments. Below is a student project that was posted on LinkedIn highlighting a positive experience and the learning from the lab.
“Over the past few weeks, I had the opportunity to develop and deploy a Python-based Network Intrusion Detection System (NIDS) capable of detecting and dynamically blocking SYN flood attacks on an FTP server.
Successfully demonstrated a complete cycle: from traffic generation → attack simulation → machine learning detection → automated defense. All built from scratch using Python and open-source libraries.”- John Bob, MITS 2025
The Mission Ahead
The threats targeting critical infrastructure are growing in sophistication and frequency. Nation-state actors, ransomware operators, and supply chain adversaries are all converging on the OT environment, and the traditional IT security playbook does not translate directly to systems where availability is paramount, and a misconfigured patch can shut down a physical process.
At Ohio University's ITS Cybersecurity Labs, we are building the tools, the testbeds, and the talent to defend these systems. Whether your interest is in hardware security, AI-driven detection, threat modeling, or industrial systems engineering, there is a place for you in this lab. The systems that drive the world need people who know how to protect them. We are training them here.
The McClure School of Emerging Communication Technologies strives to offer the best academic programs in the IT (Information Technology), cybersecurity, the game development and the Virtual Reality/Augmented Reality (VR/AR) industries. Our programs and certificates cover numerous aspects of the rapidly changing industries of information networking, cybersecurity operations, data privacy, game development, digital animation and the academic side of esports.